Items Tagged with 'security technology'
ARTICLES
Proactive security: Identify the precursors of violence
The 2023 Annual Guarding Report: Finding the right mix of human and machine
EVENTS
IMAGE GALLERIES
4K Video Surveillance Solutions for the Enterprise
Off the tradeshow floor, what can 4K surveillance solutions do for the enterprise? These five 4K surveillance solutions are designed to take the place of multiple cameras to surveil a large area or a particularly complex environment.
Product Spotlight on Covert Surveillance
New Products Revealed for ASIS International 2016
These 10 new security and risk management products are to be showcased at this year’s ASIS International 62nd Annual Seminar & Exhibits in Orlando, Florida. From security robots that can handle patrols to multi-modal access management solutions to video surveillance tools, these products are designed to enable enterprise security leaders to make the most of their resources and better secure their assets and employees.
Product Spotlight: Integrated Intercoms for Robust Security
New intercom technology merges with surveillance, access control and more to create a more unified entryway security solution.
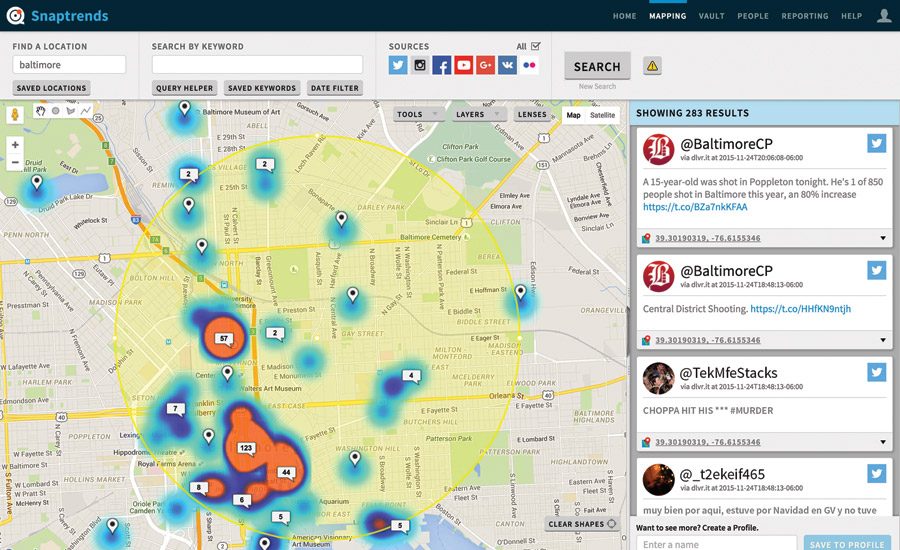
Product Spotlight: Social Media Monitoring Solutions
Facebook, Twitter, Instagram, YikYak, Weibo…. There are dozens, if not hundreds, of different social media platforms on the market today, and maintaining a grasp of your enterprise’s reputation and any potential risks in your area can be a challenge.
2016 ISC West Product Preview
Security previews 10 new security solutions to be debuted at ISC West 2016.
Product Spotlight: Visitor Management for the Enterprise
For as long as enterprises have sought to control access to facilities, there has been a need to manage visitors, vendors and other non-recurring guests. There are a number of different visitor management solutions on the market, some of which are a part of enterprise-level solutions while others are off-the-shelf software products. The products can improve the first impression a visitor forms of the organization as well as improve employee and visitor safety.
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing







.jpg?height=168&t=1708973479&width=275)


.jpg?height=168&t=1698338761&width=275)