Cyber Tactics Column
Governments and corporations are facing considerable risk to their data
Read More
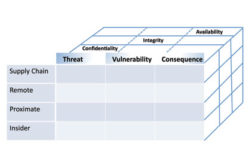
How to Reduce the Insider Cyber Threat
To best protect your company against internal abuse, it is helpful to understand the nature of the threat and to consider applying risk-based approaches to address the problem.
January 6, 2014
What to Expect When Working with Cyber Cops
What your company, as a victim of a computer intrusion, should expect when working with the Feds.
December 1, 2013
Top 5 Reasons to Report Computer Intrusions to Law Enforcement
Even when not legally required, reporting cyber crime to law enforcement can act as a deterrent for other malicious actors contemplating future attacks.
November 5, 2013
What Has Been Accomplished on Cyber Legislation?
In response to the growing cyber threat, Congress has been busy drafting legislation.
October 1, 2013
What is the Most Influential Cyber Security Team?
The Information Technology Laboratory at the National Institute of Standards and Technology is leading the charge for cyber security.
September 1, 2013
Are Public-Private Cyber Partnerships Worth the Effort?
Fifteen years after the start of the Information Sharing and Analysis Center, what have you gained?
August 1, 2013
How to Develop Cyber Security for SMEs
The cyber intrusion headlines may focus on the Fortune 100 being hacked, but they’re not the only victims.
July 1, 2013
The Top Three Cyber Security Leadership Qualities
There likely are hundreds of traits associated with great leaders.
June 1, 2013
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing